A practical setup for network observability and proactive defense on a self-hosted server.
Background
I run a web server (Ubuntu) that’s exposed to the internet — multiple apps and dashboards sit behind Nginx Proxy Manager. With growing exposure, I needed two things:
- Visibility into what’s hitting my network
- Protection against malicious IPs, bots, and brute-force attempts
That’s where ntopng and CrowdSec come in.
ntopng: Real-Time Network Traffic Monitoring
ntopng gives deep insights into traffic at the interface level — who’s connecting, what services they’re hitting, and how much data is flowing.
Setup using Docker
docker run -it --net=host \
-v /etc/ntopng:/etc/ntopng \
-v /var/lib/ntopng:/var/lib/ntopng \
ntop/ntopng:latest -i eth0Key points
--net=host: Required to access host network interfaces-i eth0: Replace with your active interface (check withip a)- Web UI: http://<your-host-ip>:3000 (default login:
admin/admin)
You can’t bind -p 3000:3000 when using --net=host. By default, the port will be opened on all interfaces. To block public access, I added an iptables rule to drop connections from the internet-facing interface (you can use any firewall tool of your choice):
iptables -A INPUT -i eth0 -p tcp --dport 3000 -j DROP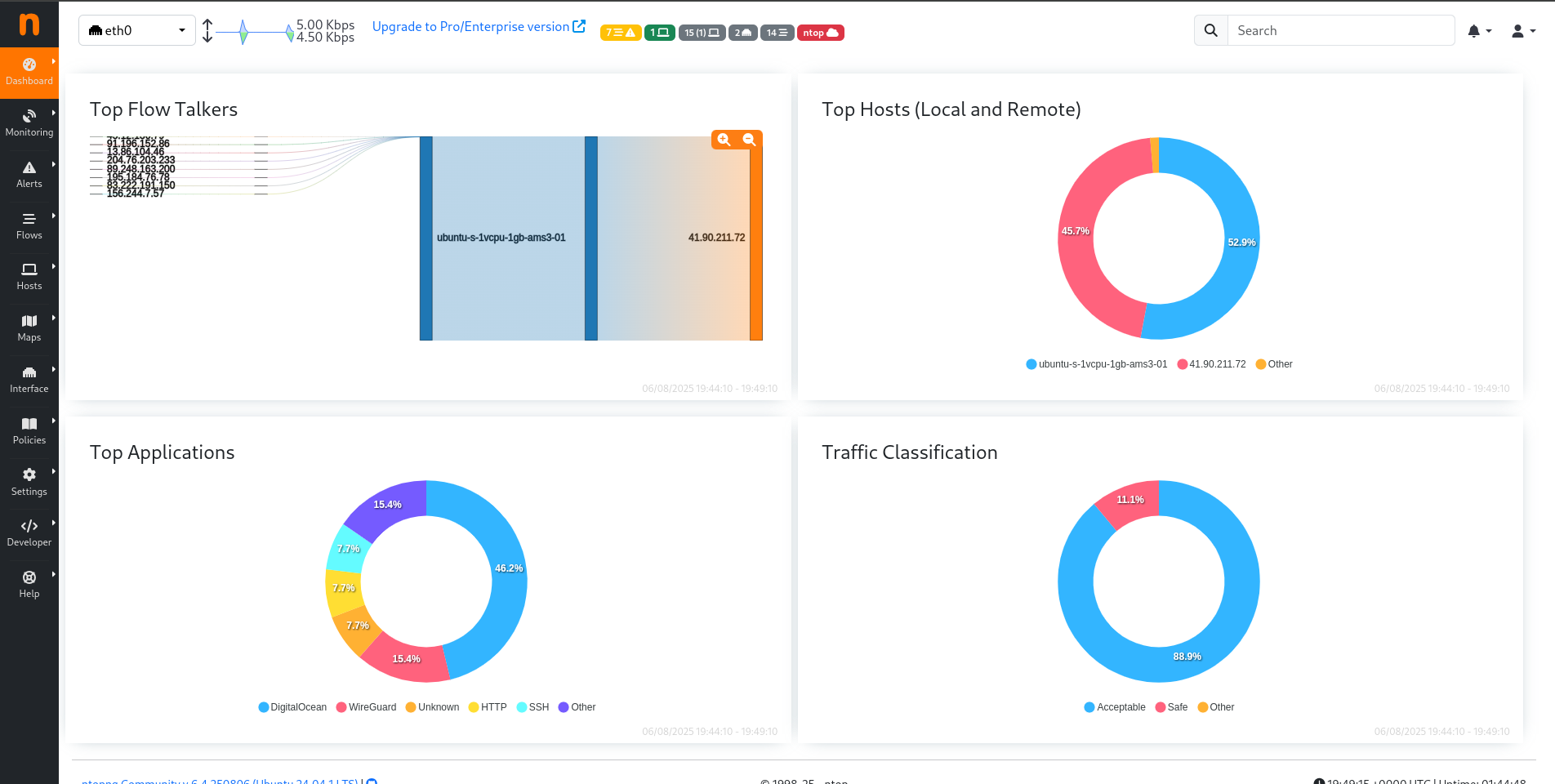
CrowdSec: Collaborative Security Engine
CrowdSec reads logs (like Nginx access logs), detects malicious patterns (e.g. brute-force, scanners) and blocks attackers automatically using bouncers.
Installing CrowdSec
Install the official repositories:
curl -s https://install.crowdsec.net | bash
Then install the security engine:
apt install crowdsecAfter install:
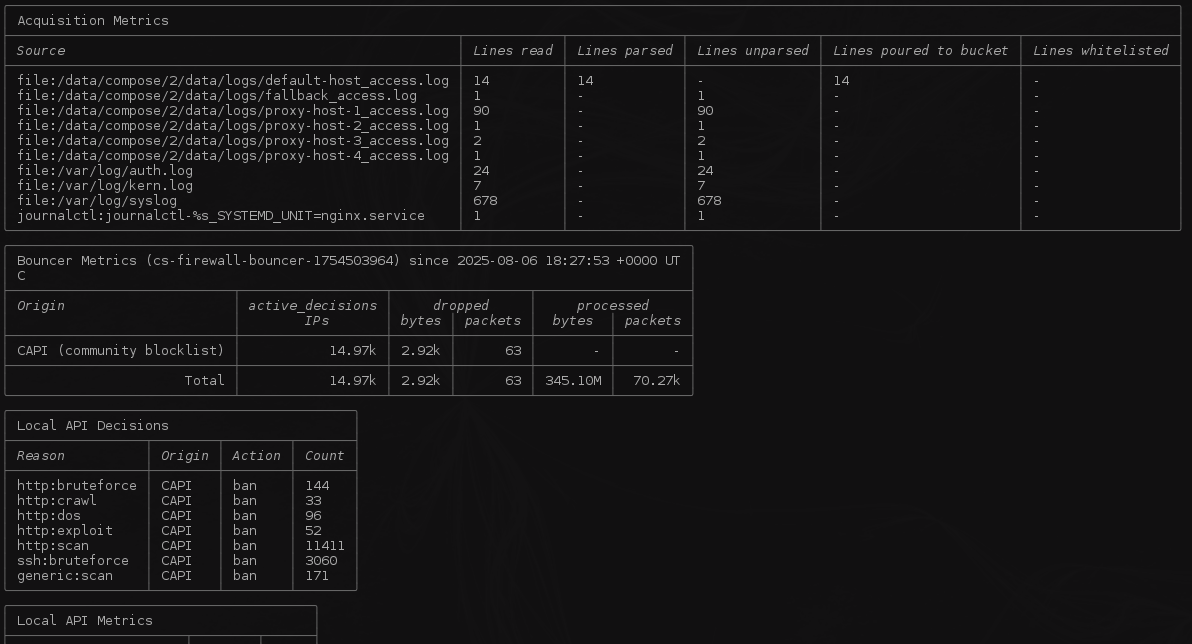
sudo cscli metrics
You should see statistics confirming the engine is active.
Configuring Log Sources
Tell CrowdSec where to find your logs. If you're using Nginx in Docker, use the bind-mounted path.
Edit /etc/crowdsec/acquis.yaml:
filenames:
- /path/to/nginx/logs/*.log
labels:
type: nginx
Restart CrowdSec:
sudo systemctl restart crowdsec
Installing Scenarios for Nginx
sudo cscli collections install crowdsecurity/nginx
This enables protections like:
- Bad bots
- Common exploit scanners
- Brute-force attempts
Blocking Malicious IPs
You need a bouncer to enforce bans. I used the iptables bouncer:
sudo apt install crowdsec-firewall-bouncer-iptables
It automatically blocks any IP flagged by the engine.
Running cscli metrics should give you something close to this:
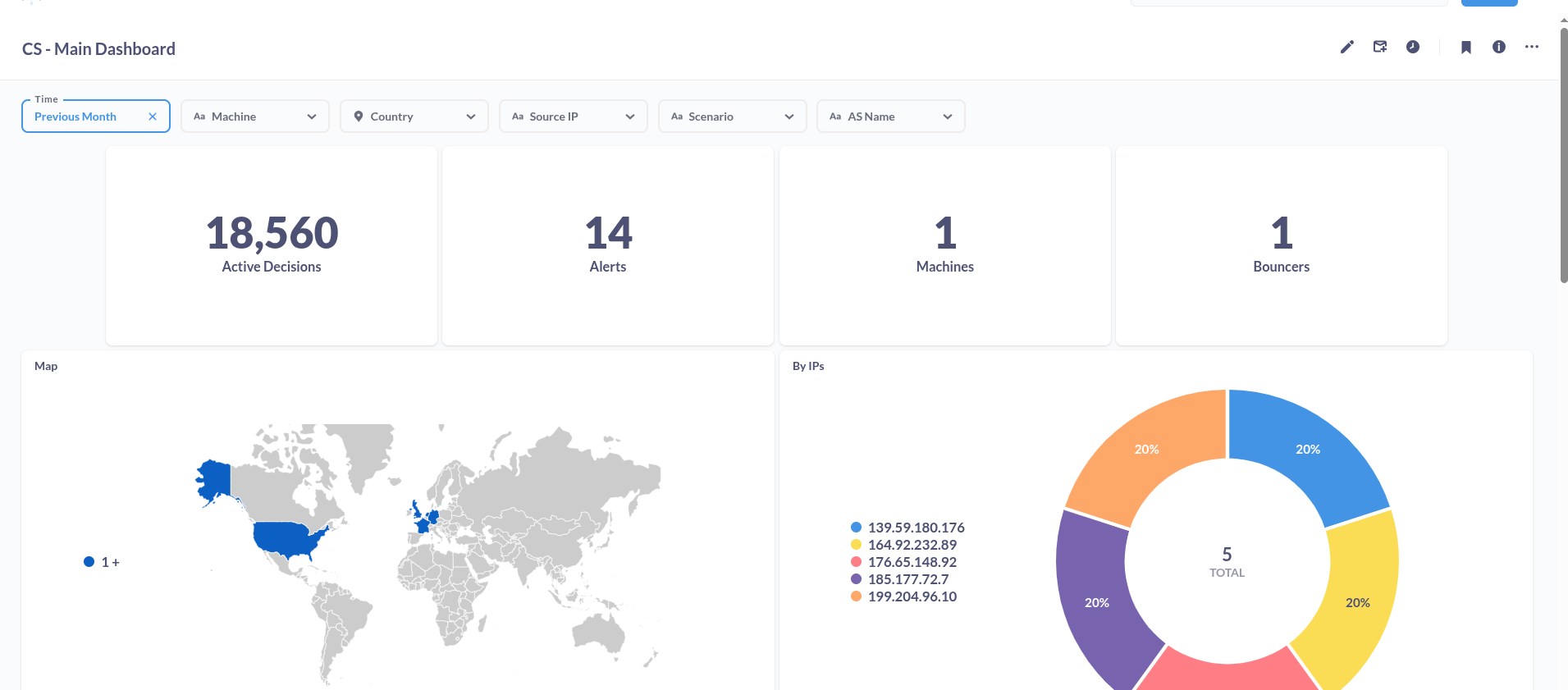
Add CrowdSec Dashboard
CrowdSec can export data to Metabase for a beautiful dashboard(Uses SQLite database by default). Run:
sudo cscli dashboard setup --listen <Your private IP> --port <desired port> --password <access password>
Access it at: http://<your-private-IP>:<desired-port>
Login credentials:
- Email:
[email protected] - Password:
<access-password>
Final Thoughts
With ntopng, I know what’s happening.
With CrowdSec, I stop what shouldn’t be.
This combo gives me solid awareness and defense — and they play nicely in a Dockerized setup.